35,000+ smart investors are already getting financial news, market signals, and macro shifts in the economy that could impact their money next with our FREE weekly newsletter. Get ahead of what the crowd finds out too late. Click Here to Subscribe for FREE.
Espionage, the art of gathering secret information or conducting covert operations, has been a staple of international intrigue for centuries.
While associated with glamorous spies and clandestine missions, foreign espionage is not confined to the pages of spy novels or the screens of Hollywood movies.
In today’s interconnected world, it’s closer to home than you might think. Let’s explore 14 ways foreign espionage is infiltrating American neighborhoods, often without our knowledge.
Cyber Espionage
Closer Than You Think: 14 Shocking Instances of Foreign Espionage in American Communities
- Cyber Espionage
- Social Engineering
- Infiltration of Educational Institutions
- Economic Espionage
- Influence Campaigns
- Spying on Immigrant Communities
- Hacking Government Systems
- Industrial Espionage
- Espionage via Diplomatic Missions
- Espionage through Supply Chains
- Recruitment of Agents
- HUMINT Operations
- Use of Front Companies
- Espionage in High-Tech Hubs
- Conclusion
- Don’t Toss It Yet: 12 Overlooked Antiques In Your Home That Could Make You An Overnight Millionaire
- Profitable Stock Traders are Using This Tool to “Hack” the Markets
- 10 Industries That Will Make The Most Millionaires In The Next 5 Years
- 8 Cryptos Set to Shoot to the Moon in 2023 – One Small Investment, One Giant Leap for Your Wallet
- 10 Stocks in Bill Gates Stock Portfolio Smart Investors are Buying
- The 27 Unexpected Habits Of The Wealthy: Secrets To Maximize Your Money

Foreign governments use sophisticated cyberattacks to infiltrate American businesses, government agencies, and infrastructure. These attacks aim to steal sensitive data, compromise security, and gain a strategic advantage.
With the rise of digital technology, cyber espionage has become one of the most insidious and prevalent forms of foreign spying. State-sponsored hackers from nations such as Russia, China, and North Korea continuously probe American computer systems for vulnerabilities.
In recent years, we’ve witnessed high-profile breaches like the Equifax data breach, where millions of Americans’ personal information was exposed. This illustrates how foreign actors may also attack private companies that hold critical data.
Social Engineering

Foreign agents may trick people into disclosing private information by using social engineering techniques like phishing emails and phony social media pages. The human element of espionage remains a potent weapon in the spy’s toolkit.
Foreign agents can gain access to confidential information or infect our machines with malware by taking advantage of our confidence and readiness to divulge information.
Infiltration of Educational Institutions

Targeting universities, research centers, and academic institutions to gain access to cutting-edge research and technology is another practice. Educational institutions are hubs of innovation and research, making them attractive targets for espionage.
Foreign governments often seek to exploit the open exchange of knowledge and ideas, sometimes by recruiting students or faculty members as informants.
Economic Espionage

One prevalent method of foreign espionage is the theft of trade secrets and proprietary information, putting American companies at economic risk. To obtain a competitive edge, American businesses make significant investments in research and development.
This leaves them highly susceptible to economic espionage. Foreign actors make considerable effort to infiltrate American corporations and steal important trade secrets.
Influence Campaigns

Foreign actors engage in propaganda and disinformation campaigns to manipulate public opinions and influence American politics and policies. Social media and digital communication are the battleground for such campaigns.
These campaigns amplify extremist views, create a divide amongst the masses, and influence electoral outcomes. It’s not just about stealing secrets; it’s about shaping the narratives that guide our nation’s choices.
Spying on Immigrant Communities

Some foreign governments keep tabs on their expatriate communities in the United States, potentially coercing or recruiting individuals to spy on fellow immigrants or engage in covert activities.
Immigrant communities maintain strong ties to their countries of origin. This connection can be exploited to gather information and even recruit agents from within these communities.
Hacking Government Systems

Foreign intelligence services may target federal, state, and local government systems to access classified information and disrupt operations. The political, military, and intelligence apparatus of the United States are prime targets for espionage.
From attempts to breach sensitive military networks to hacking voter registration systems, foreign actors aim to gather classified information and influence government policies. The recent SolarWinds hack, attributed to Russian hackers, exposed vulnerabilities in government systems.
Industrial Espionage

The theft of intellectual property, research, and technology threatens American innovation and industry leadership. Espionage also targets American business interests.
Foreign actors infiltrate corporations to steal intellectual property, be it the formula for a groundbreaking drug or the design of cutting-edge technology. The economic consequences of industrial espionage can be devastating on multiple fronts.
Espionage via Diplomatic Missions

Foreign embassies and consulates can house intelligence officers tasked with espionage, such as collecting information on American policies, security, and trade.
While diplomatic missions are meant for diplomacy, they can serve as a cover for intelligence officers engaging in covert operations.
These operatives gather information as required by their governments. The use of diplomatic immunity can make it difficult for U.S. authorities to counter their activities at home.
Espionage through Supply Chains

Infiltration of supply chains allows foreign actors to insert compromised products or components into the American market, creating vulnerabilities in critical infrastructure. The global nature of modern supply chains presents both opportunities and risks.
They can exploit these supply chains to smuggle products and people. These products can include anything from defective electronics with backdoors to counterfeit pharmaceuticals, putting American consumers and businesses at risk.
Recruitment of Agents

Foreign intelligence agencies actively recruit American citizens or residents, leveraging their access to sensitive information or institutions. Foreign governments try to turn Americans into assets by recruiting them.
Whether it’s through financial incentives, ideological alignment, or coercion, these recruits can provide valuable information on a wide range of subjects, from military plans to government policies.
HUMINT Operations

Human Intelligence (HUMINT) involves foreign agents building relationships with individuals who can provide valuable information, sometimes exploiting personal vulnerabilities or motivations.
Despite advanced spying technologies, the human factor remains irreplaceable. Foreign agents employ HUMINT to develop relationships with individuals who can provide valuable information. These relationships may be built on trust, personal motivations, or even exploiting vulnerabilities or secrets of the targeted individuals.
Use of Front Companies

Front companies can serve as a cover for espionage activities, enabling foreign governments to operate within the United States without arousing suspicion. To operate covertly within the United States, they use front companies.
These businesses appear legitimate on the surface but serve as covers for espionage operations. They can engage in various activities, from intelligence gathering to technology theft.
Espionage in High-Tech Hubs

Foreign operatives may focus on cities like Silicon Valley, where they can target startups and tech giants, seeking to steal technology and intellectual property. High-tech hubs, like Silicon Valley, are hotbeds of innovation and technological advancement.
Foreign operatives are keen to infiltrate these regions to steal cutting-edge technology and intellectual property. The competition for innovation and intellectual property rights is fierce, and espionage becomes a weapon of choice for achieving technological dominance.
Conclusion

Foreign espionage isn’t just a tale of spies and covert operations. It’s a complex web of activities that can have far-reaching consequences for American security, businesses, and individuals.
Staying informed about these threats and protecting sensitive information is crucial in safeguarding the nation from these unseen frontlines of espionage.
As technology evolves and global relationships continue to shift, understanding and addressing these risks becomes even more critical for the safety and security of the United States and its citizens.
The fight against foreign espionage is ongoing, and awareness is the first step towards safeguarding the nation from these hidden threats. Vigilance from all levels can help stop any such activities before they damage the nation.
Don’t Toss It Yet: 12 Overlooked Antiques In Your Home That Could Make You An Overnight Millionaire

Antique items have long captured the fascination of collectors and enthusiasts, and beyond their sentimental value, they hold the potential to bring considerable wealth to their fortunate owners.
Here are the 12 Overlooked Antiques In Your Home That Could Make You An Overnight Millionaire
Profitable Stock Traders are Using This Tool to “Hack” the Markets

This tool is helping traders beat the market compared to those who have no idea what is.
Here are the Top 28 Stock Trading Discord Servers Right Now.
10 Industries That Will Make The Most Millionaires In The Next 5 Years

If you are not paying attention to these 10 industries, you are about to miss out on the next boom of millionaires.
See the 10 Industries About to Make the Most Millionaires in the Next 5 Years.
8 Cryptos Set to Shoot to the Moon in 2023 – One Small Investment, One Giant Leap for Your Wallet

These are 8 cryptocurrencies you need to know about before you miss out on the next boom.
8 Cryptos Set to Shoot to the Moon in 2023 – One Small Investment, One Giant Leap for Your Wallet
10 Stocks in Bill Gates Stock Portfolio Smart Investors are Buying
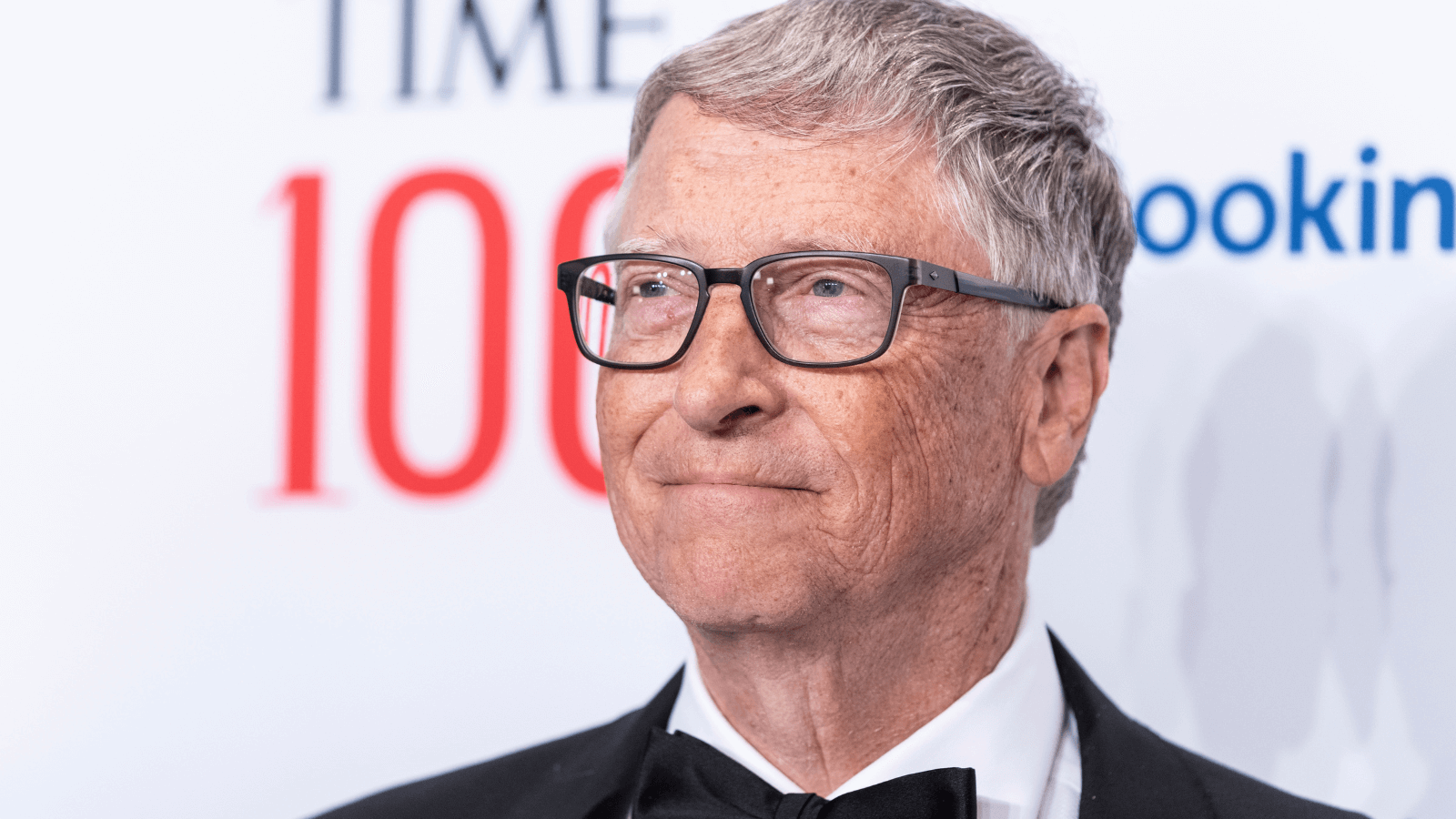
We share the top 10 stocks that Bill Gates owns that smart investors are buying right now.
10 Stocks in Bill Gates Stock Portfolio Smart Investors are Buying
The 27 Unexpected Habits Of The Wealthy: Secrets To Maximize Your Money

The wealthiest people on Earth share similarities in their habits. We break down the 27 habits you would not expect!
The 27 Unexpected Habits Of The Wealthy: Secrets To Maximize Your Money
This Options Discord Chat is The Real Deal
While the internet is scoured with trading chat rooms, many of which even charge upwards of thousands of dollars to join, this smaller options trading discord chatroom is the real deal and actually providing valuable trade setups, education, and community without the noise and spam of the larger more expensive rooms. With a incredibly low-cost monthly fee, Options Trading Club (click here to see their reviews) requires an application to join ensuring that every member is dedicated and serious about taking their trading to the next level. If you are looking for a change in your trading strategies, then click here to apply for a membership.
